Patient Privacy Monitoring
The System is Loaded with 15 Out of the Box Proactive Alerts and Ready Made Reports to Optimize Your User Access Monitoring and Patient Privacy Monitoring Program

Features And Benefits

Evaluating Access From Raw Data Logs is a Daunting Task
Evaluating access from raw data logs is a daunting task. This is especially true if it has to be done manually from single or multiple EHR feeds such as Epic/Cerner, Allscripts, PACS etc. The effort causes additional time and resourcing spent researching. Reviewing and determining the events and story pertaining to the users actions based on their use of metrics/routine names.
The use of an audit tool can actually help take unstructured raw data and weave it into an intricate fabric. Allowing for patterns and anomalies to be seen. This provides the investigator a comprehensive story of both the user’s activities and of the patient’s care flow. And documentation and cataloging of the work done can be shown for proactive monitoring.
With Intruno Patient Privacy Monitoring, healthcare organizations gain proactive tools to improve patient data security and regulatory compliance.
Key Advantages Includes
- Single repository for all investigations and alerts
- Customized workflows fitted to your Privacy & Compliance programs
- Expert consultants to evaluate your program and recommend best practices
- Summary Analytics: Monthly, Annual or Custom reports on violation trends
- Readily available OCR audit support
- Support to your Privacy & Compliance teams to free up resources
Intruno Helps Healthcare Organizations To Proactively Ensure Patient Privacy And Regulatory Compliance
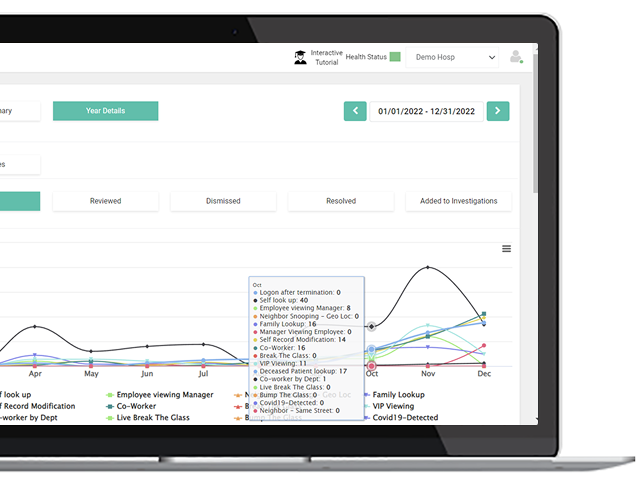
Proactive Detection & Analysis
Intruno’s healthcare privacy solution automatically identifies and reports user access risks to protect patient privacy. Privacy Analysts will not have to manually search for inappropriate or unapproved use of Patient data, which can be akin to ‘finding a needle in a haystack.’ With fully automatic integration, Privacy & Compliance teams do not have to rely on IT teams to provide reports for further analysis. All data is available in a single dashboard panel.
Automatic Detection of Policy Violations
Our proprietary AI Machine Learning algorithms automatically understand the appropriate job duties of each person, and their peers accessing patient data. This enables the accurate detection and reporting of inappropriate user activities which put patient privacy at risk.
Comprehensive Incident/investigation Management System to Track and Maintain a Forensic Repository
It’s important to understand typical user work patterns. Having a clear picture of what is routine and what is anomalous can help uncover potentially noncompliant and risky activities even if they are unintentional.
User Profile Showing Across EMR Applications
The output is a digital signature of every user’s normal behavior across each EMR application within the organization. The product provides 24/7 monitoring; for all users, across your entire EMR ecosystem. As it monitors user behavior, it continuously learns, recognizes and remembers normal patterns of use – to immediately identify activities which deviate from normal patterns.

How Does It Work?
Who Are The Conventional Users Of The Intruno Platform ?

Chief Security Officer/ CIO
Intruno helps your team to perform security risk assessments, track data breach investigations and enables you to provide input into privacy & breach investigation cases from an IT security perspective.

Compliance Officer/ Privacy Officer
Intruno helps you to perform executive level review of cases & investigations, track litigations and ensure the organization’s compliance with various State & Federal regulations.
Would You Like to See How Intruno Can Help Your Organization?